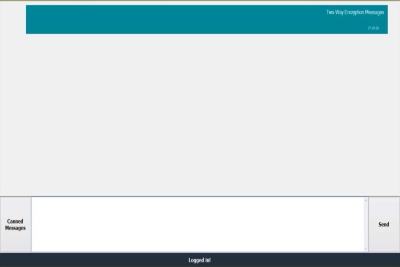
End-to-end encryption (E2EE)
End-to-end encryption (E2EE) is a method used for securing encrypted data while it is moving from the source to the destination. The objective of end-to-end encryption is to encrypt data at the Web level and to decrypt it at the database or application server. It can solve the problem of revealing data while net sniffing if a Web server has been compromised. If implemented with trusted algorithms, end-to-end encryption can provide the highest level of data protection.
In end-to-end encryption, the user initiates the encryption from a source device. This also provides greater flexibility to the user in deciding which data to encrypt. In this encryption method, the routing information, addresses, headers, and trailers are not encrypted. Moreover, at each hop in the network, the headers and trailers do not undergo decryption or encryption. The hop computers read the routing information and pass on the data packets to their path..

A separate key is not required for the decryption of the packet data in the hop computer on the network.

Greater flexibility to the user in deciding which data to encrypt. Selective encryption provides great help in the case of sensitive data. The availability of choosing specific configurations helps in higher modularization of the functionality.
FEATURES AND CAPABILITIES
The advantages of end-to-end encryption are as follows::
• A separate key is not required for the decryption of the packet data in the hop computer on the network.
• Greater flexibility to the user in deciding which data to encrypt. Selective encryption provides great help in the case of sensitive data. The availability of choosing specific configurations helps in higher modularization of the functionality.
• The file size involved is smaller, and the processing uses only a minimal yet sufficient set of resources and encryption time.
• The routing information, headers, and trailers are protected as they are encrypted.